Security Group
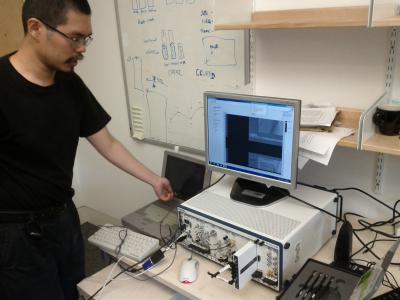
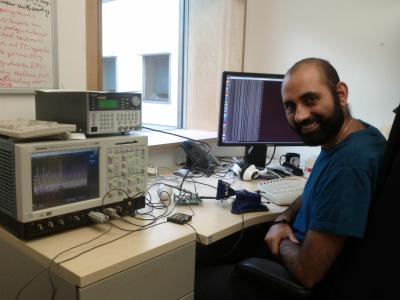
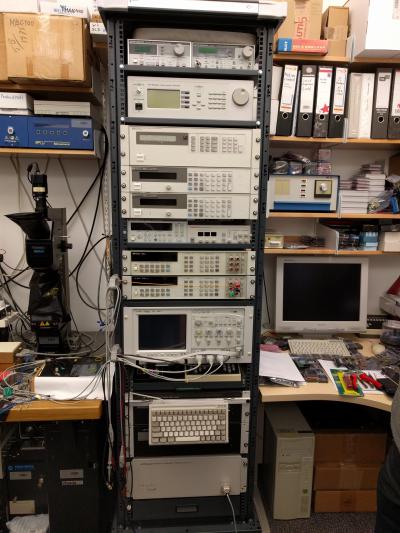
TAMPER Laboratory
Contents |
The TAMPER (Tamper And Monitoring Protection Engineering Research) Lab at the University of Cambridge Department of Computer Science and Technology focuses on the hardware aspects of computer and communication security.
Experience shows that the most commonly exploited vulnerabilities in modern information security systems result from implementation defects, user errors and poorly understood characteristics of computer hardware. Hardware security is a particularly neglected field.
Hardware vendors have often made claims about the tamper resistance or even the correct functioning of their products which turned out to be unjustified, and the lack of published information about attack techniques made it difficult for customers to evaluate their claims. This has led to widespread and expensive security failures in applications such as pay-TV and banking. Yet we see the designers of newly fielded systems making the mistakes over and over again.
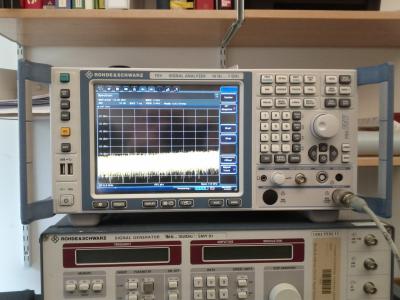
Research in hardware security requires a broad range of capabilities. This includes not only classical cryptography and computer security know-how, but also expertise in physics, electronics, chemistry, material sciences, microelectronics, communication systems and signal processing. It often requires the construction of specialised equipment, and it usually takes some practice to acquire laboratory skills - especially where attacks involve techniques such as microprobing silicon chips, analysing unintended radio frequency emanations or the disassembly of software.
In the TAMPER Lab, we study existing security products, document how they have been penetrated in the past, develop new attack techniques, and try to forecast how newly available technologies will make it easier to bypass hardware security mechanisms. We then develop and evaluate new countermeasures and assist industrial designers in staying ahead of the game, most of all by giving them an advanced understanding of which attack techniques are most dangerous. We are especially interested in protection systems for mass-market applications, and in forensic applications.
We have in-depth expertise in semiconductor and emissions security. We are also interested in biometrics, physical seals, signal remanence in storage media, and whatever other technologies come along that may be useful to attack, defence or both.
People
- Markus Kuhn — compromising emanations, power analysis, VLSI reverse engineering, smartcard security, conditional access and e-cash applications, bus-encryption processors, low-cost attacks, biometric identification
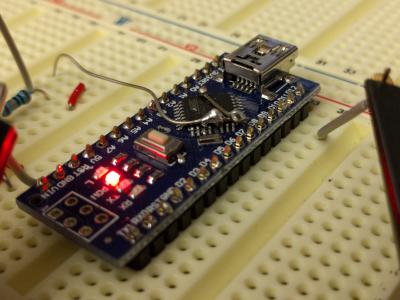
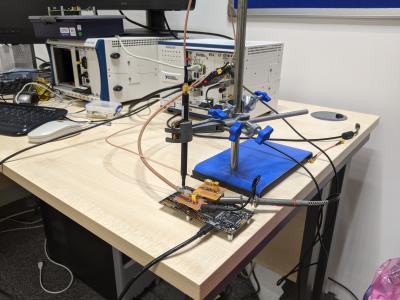
- Sergei Skorobogatov — microcontroller, FPGA and memory security, data remanence, optical attacks, side-channel attacks, reverse engineering, NVM remanence, local heating attacks, optical emission analysis, hardware assurance, physical tampering
Compromising emanations / emissions security / side-channel attacks
What can we learn from a system (whether an office PC or a smartcard) by studying the electromagnetic, optic, acoustic and other signals that it emits? How can we either suppress the information leakage, or (if we are the attacker) covertly broadcast secrets over large distances?
Selected publications
- Dimitrije Erdeljan, Markus G. Kuhn: Benefits of coherent demodulation for eavesdropping on HDMI emissions. EMC Europe 2024, 2–5 September 2024, Bruges, Belgium. (slides)
- Shih-Chun You, Markus G. Kuhn, Sumanta Sarkar, Feng Hao: Low trace-count template attacks on 32-bit implementations of ASCON AEAD. IACR Transactions on Cryptographic Hardware and Embedded Systems (TCHES), Vol. 2023, No 4, pp 344–366, August 2023. (data set)
- Shih-Chun You, Markus G. Kuhn: Single-trace fragment template attack on a 32-bit implementation of Keccak. CARDIS 2021, 11–12 November 2021, Lübeck, Springer, LNCS 13173, pp 3–23, 2022. DOI: 10.1007/978-3-030-97348-3_1
- Shih-Chun You, Markus G. Kuhn: A template attack to reconstruct the input of SHA-3 on an 8-bit device. Presented at COSADE 2020, 5–7 October 2020, Springer, LNCS 12244, pp 25-42. DOI: 10.1007/978-3-030-68773-1_2
- Marios O. Choudary, Markus G. Kuhn: Efficient, portable template attacks. IEEE Transactions on Information Forensics and Security, Vol 13, No 2, February 2018, pp 490-501, DOI 10.1109/TIFS.2017.2757440
- Marios O. Choudary, Markus G. Kuhn: Efficient stochastic methods: profiled attacks beyond 8 bits. CARDIS 2014, LNCS 8968, pp. 85–103, 2015. DOI: 10.1007/978-3-319-16763-3_6
- Omar Choudary, Markus G. Kuhn: Template attacks on different devices. COSADE 2014, LNCS 8622, pp. 179–198, 2014. DOI: 10.1007/978-3-319-10175-0_13
- Omar Choudary, Markus G. Kuhn: Efficient template attacks. CARDIS 2013, LNCS 8419, pp. 253–270, 2014.
- Markus G. Kuhn: Compromising emanations of LCD TV sets, IEEE Transactions on Electromagnetic Compatibility, Vol. 55, No. 3, pp 564–570, June 2013. DOI: 10.1109/TEMC.2013.2252353
- Sergei Skorobogatov, Christopher Woods: In the blink of an eye: There goes your AES key. IACR Cryptology ePrint Archive, Report 2012/296, May 2012
- Sergei Skorobogatov: Synchronization method for SCA and fault attacks. Journal of Cryptographic Engineering (JCEN), Ed: Cetin K. Koc, Vol. 1, Issue 1, Springer, April 2011, pp 71-77
- Sergei Skorobogatov: Using Optical Emission Analysis for Estimating Contribution to Power Analysis. 6th Workshop on Fault Diagnosis and Tolerance in Cryptography (FDTC 2009), September 2009, Lausanne, Switzerland. IEEE-CS Press, ISBN 978-0-7695-3824-2, pp 111-119
- Markus G. Kuhn: Security Limits for Compromising Emanations. J.R. Rao, B. Sundar (Eds.): Workshop on Cryptographic Hardware and Embedded Systems (CHES 2005), August 2005, Edinburgh, Scotland, LNCS 3659, pp 265-279
- Markus G. Kuhn: Compromising emanations: eavesdropping risks of computer displays. Technical Report UCAM-CL-TR-577, University of Cambridge, Computer Laboratory, December 2003
- Markus G. Kuhn: Optical Time-Domain Eavesdropping Risks of CRT Displays, Proceedings of the 2002 IEEE Symposium on Security and Privacy, Oakland, California, May 2002. (FAQ)
- Markus G. Kuhn, Ross J. Anderson: Soft Tempest: Hidden Data Transmission Using Electromagnetic Emanations, in David Aucsmith (Ed.): Information Hiding, Second International Workshop, IH'98, Portland, Oregon, USA, April 1998, Proceedings, LNCS 1525, Springer-Verlag, ISBN 3-540-65386-4, pp 124-142
Posters
- Shih-Chun You, Markus G. Kuhn, Sumanta Sarkar, Feng Hao: A Template Attack on ASCON AEAD. CHES 2022, Leuven, Belgium.
- Sergei Skorobogatov: Optical surveillance on silicon chips. November 2009
- Sergei Skorobogatov: Power analysis attacks. October 2006
- Markus G. Kuhn: Optical remote eavesdropping risks of CRT displays. August 2002
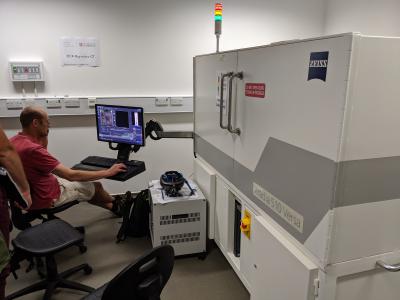
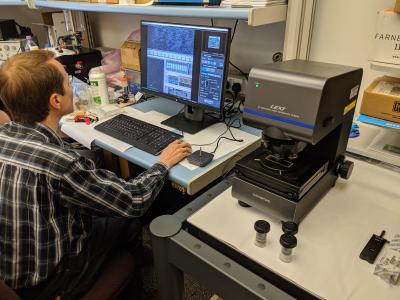
Semiconductor security
How can we extract software from a security processor or otherwise reconstruct cryptographic keys stored in it? This may involve invasive techniques where we decapsulate the chip package and use semiconductor test equipment to probe, modify and interfere with the die; it may also involve non-invasive techniques such as monitoring electromagnetic leakage and inducing faults using power transients and similar techniques.
Some extreme cases lie at the intersection of Hardware Security with Failure Analysis and Forensic Analysis. Imagine a situation where the embedded software and data need to be recovered from a chip exposed to electric shock, high temperature and strong mechanical force. Recovering any information from a die cracked in half with burned I/O pads sounds unrealistic, while 100% success rate would be impossible. Nevertheless, our ongoing research is aimed at solving this challenge.
Selected Publications
- Sergei Skorobogatov: Deep dip teardown of tubeless insulin pump. arXiv:1709.06026, September 2017
- Sergei Skorobogatov: How microprobing can attack encrypted memory. Euromicro Conference on Digital System Design, AHSA 2017, 30 August - 1 September 2017, Austria, IEEE Computer Society
- Franck Courbon, Sergei Skorobogatov, Christopher Woods: Reverse engineering Flash EEPROM memories using Scanning Electron Microscopy. Proceedings of the 15th Smart Card Research and Advanced Application Conference (CARDIS 2016), Cannes, France, November 2016
- Franck Courbon, Sergei Skorobogatov, Christopher Woods: Direct charge measurement in Floating Gate transistors of Flash EEPROM using Scanning Electron Microscopy. 42nd International Symposium for Testing and Failure Analysis (ISTFA), November 2016
- Sergei Skorobogatov: The bumpy road towards iPhone 5c NAND mirroring. arXiv:1609.04327, September 2016
- Mike Bond, Omar Choudary, Steven J. Murdoch, Sergei Skorobogatov, Ross Anderson: Be prepared: The EMV pre-play attack. IEEE Security & Privacy, pp 56-64, March 2015
- Mike Bond, Omar Choudary, Steven J. Murdoch, Sergei Skorobogatov, Ross Anderson: Chip and Skim: cloning EMV cards with the pre-play attack. IEEE Symposium on Security and Privacy ("Oakland"), May, 2014
- Mike Bond, Omar Choudary, Steven J. Murdoch, Sergei Skorobogatov, Ross Anderson: Chip and Skim: cloning EMV cards with the pre-play attack. arXiv 0547955, September 2012
- Sergei Skorobogatov: Flash Memory 'Bumping' Attacks. Cryptographic Hardware and Embedded Systems Workshop (CHES-2010), August 2010, LNCS 6225, Springer-Verlag, ISBN 3-642-15030-6, pp 158-172
- Sergei Skorobogatov: Optical Fault Masking Attacks. 7th Workshop on Fault Diagnosis and Tolerance in Cryptography (FDTC 2010), August 2010, Santa Barbara, USA. IEEE-CS Press, ISBN 978-0-7695-4169-3, pp 23-29
- Sergei Skorobogatov: Local Heating Attacks on Flash Memory Devices. 2nd IEEE International Workshop on Hardware-Oriented Security and Trust (HOST-2009), July 2009, San Francisco, CA, USA. IEEE Xplore, ISBN 978-1-4244-4804-3
- Sergei Skorobogatov: Optically Enhanced Position-Locked Power Analysis. Cryptographic Hardware and Embedded Systems Workshop (CHES-2006), LNCS 4249, Springer-Verlag, October 2006, Yokohama, Japan, ISBN 3-540-46559-6, pp 61-75
- Sergei Skorobogatov: Data Remanence in Flash Memory Devices. Cryptographic Hardware and Embedded Systems Workshop (CHES-2005), LNCS 3659, Springer-Verlag, August 2005, Edinburgh, Scotland, ISBN 3-540-28474-5, pp 339-353
- Sergei Skorobogatov: Semi-invasive attacks – A new approach to hardware security analysis. Technical Report UCAM-CL-TR-630, University of Cambridge, Computer Laboratory, April 2005
- Sergei P. Skorobogatov, Ross J. Anderson: Optical Fault Induction Attacks, Cryptographic Hardware and Embedded Systems Workshop (CHES-2002), San Francisco, CA, USA, August 2002 (slides)
- David Samyde, Sergei Skorobogatov, Ross Anderson, Jean-Jacques Quisquater: On a New Way to Read Data from Memory, First International IEEE Security in Storage Workshop, December 2002, Greenbelt Marriott, Maryland, USA
- Sergei Skorobogatov: Low temperature data remanence in static RAM, University of Cambridge, Computer Laboratory, Technical Report UCAM-CL-TR-536, June 2002
- Oliver Kömmerling, Markus G. Kuhn: Design Principles for Tamper-Resistant Smartcard Processors, USENIX Workshop on Smartcard Technology, Chicago, Illinois, USA, May 1999 (slides)
- Markus G. Kuhn: Cipher Instruction Search Attack on the Bus-Encryption Security Microcontroller DS5002FP. IEEE Transactions on Computers, Vol 47, No 10, October 1998, pp 1153-1157
- Ross J. Anderson, Markus G. Kuhn: Low Cost Attacks on Tamper Resistant Devices, in M. Lomas et al. (ed.): Security Protocols, 5th International Workshop, Paris, France, April 1997, Proceedings, Springer, LNCS 1361, ISBN 3-540-64040-1, pp 125-136
- Ross J. Anderson, Markus G. Kuhn: Tamper Resistance - a Cautionary Note, The Second USENIX Workshop on Electronic Commerce Proceedings, Oakland, California, November 1996, ISBN 1-880446-83-9, pp 1-11
Posters
- Sergei Skorobogatov: Optically enhanced position-locked power analysis. October 2006
- Sergei Skorobogatov: Data remanence in non-volatile semiconductor memory (Part II). July 2006
- Sergei Skorobogatov: Data remanence in non-volatile semiconductor memory (Part I). October 2004
- Sergei Skorobogatov: Video imaging of silicon chips. March 2004
- Sergei Skorobogatov: Hardware Security. January 2003
Hardware assurance and reliability
With the growing complexity of integrated circuits the importance of post production testing and functional verification is growing. This is necessary to address the issues in failure analysis and to perform design verification for correctness, and to eliminate inevitable bugs. Another important question to answer is whether the device be fully functional in 10, 20 or 50 years time? Not only it is important that the hardware does what it is supposed to, but also whether the hardware has any additional and sometime unintentional functionality. This could be in the form of disguised factory test or debug interface, silicon level backdoor or deliberately inserted Trojan. Most silicon chips are now designed and made abroad by third parties. Is there any independent way to evaluate these products that are used in critical systems? Until the development of the efficient silicon scanning techniques, it would be unfeasible to test real silicon chips for Trojans or backdoors.
Selected Publications
- Sergei Skorobogatov, Christopher Woods: Breakthrough silicon scanning discovers backdoor in military chip. Cryptographic Hardware and Embedded Systems Workshop (CHES-2012), September 2012, LNCS 7428, Springer, ISBN 978-3-642-33026-1, pp 23-40
Posters
- Sergei Skorobogatov: Silicon scanning reveals hidden backdoors in semiconductor chips. March 2013