CTSRD
CTSRD – Rethinking the hardware-software interface for security
PIs: Robert N. M. Watson (University of Cambridge), Simon W. Moore (University of Cambridge), Peter Sewell (University of Cambridge), Brooks Davis (SRI International) and Peter Neumann (SRI International)
September 2023: We have posted CHERI ISAv9, which replaces CHERI-MIPS with CHERI-RISC-V as our primary reference architecture, CHERI-MIPS is removed, merged register files are always used, tags are cleared in preference to exception throwing for non-monotonic capability modification, and DDC/PCC no longer relocate memory accesses by default. CHERI-RISC-V is substantially refined in preparation for standardisation. The CHERI-x86 sketch is now substantially more detailed. |
January 2022: Arm has shipped its CHERI-enabled Morello prototype processor, SoC, and board! Read blog posts about this at Arm and Microsoft, and our own thoughts at Cambridge. |
Learn about the CHERI architecture! Our technical report An Introduction to CHERI is a high-level summary of our work on CHERI architecture, microarchitecture, formal modeling, and software.
Clean Slate Trustworthy Secure Research and Development (CTSRD - pronounced "custard") is a joint research project between SRI International's Computer Science Laboratory and the University of Cambridge Computer Laboratory, supported by DARPA (part of the DARPA CRASH, MRC, and SSITH programmes), Google, and Arm. The project is revisiting the hardware-software security interface for general-purpose CPUs to fundamentally improve security; to this end, we are integrating a hybrid capability model and continuous hardware-assisted validation of security design principles with a commodity CPU ISA and open source operating systems. We are pursuing several new software/hardware features as part of this research:
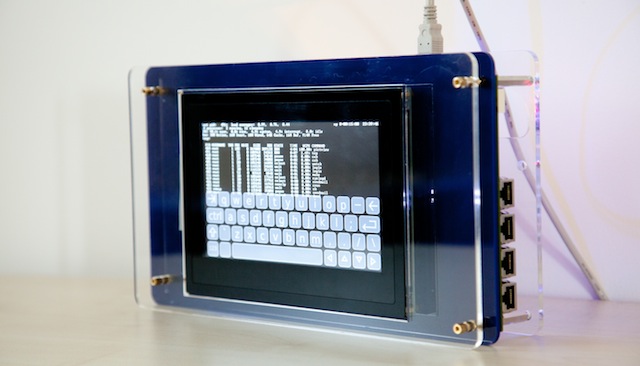
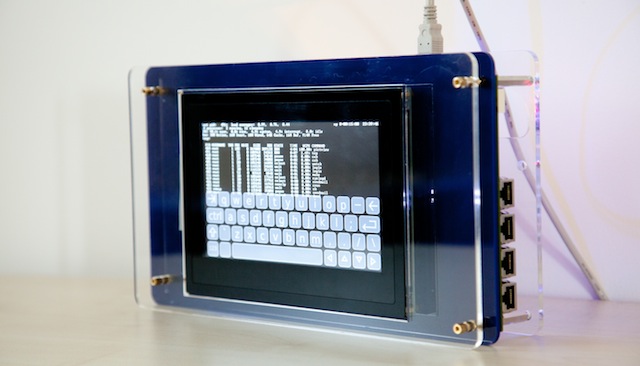
- BERI: a open-source hardware-software research and teaching platform: a 64-bit RISC processor implemented in the high-level Bluespec hardware description language (HDL), along with compiler, operating system, and applications;
- CHERI: capability hardware enhanced RISC instructions : hardware-accelerated in-process memory protection and sandboxing model based on a hybrid capability model;
- TESLA: temporally enforced security logic assertions: compiler-generated runtime instrumentation continuously validating temporal security properties;
- SOAAP: security-oriented analysis of application programs: automated program analysis and transformation techniques to help software authors utilize Capsicum and CHERI features; and
- Smten: SMT-based tools to support the formal verification of processor designs implemented in Bluespec.
There is a strong interest, throughout, in judiciously applying formal methodology and bringing formally grounded techniques to mainstream hardware and software development. This work has motivated the creation of the Bluespec extensible RISC implementation – an open-source platform for research into the hardware-software interface, with a BSD-licensed operating system and toolchain based on FreeBSD and Clang/LLVM. We are using open source, wherever possible, to transition new technologies into mainstream use.
CTSRD builds on long past experience at both institutions in security and systems research, including Multics, PSOS, the Newcastle DSS, separation kernels, the DARPA CHATS programme, PVS/SAL/YICES, LynuxWorks, the CAP computer, the MAC Framework, multi-threaded CPU design, Xen, Capsicum, and MirageOS.
News media
- The New Scientist, August 2018: Uncrackable computer chips stop malicious bugs attacking your computer - This article describes CHERI and other projects focusing on more secure computer architectures.
- The Economist, June 2014: Hiding from Big Data - Robert Watson explains how compartmentalised software designs could have mitigated Heartbleed.
- New York Times, October 2012: article on Dr Peter G. Neumann regarding clean-slate research for security.
- ACM Queue, October 2012: interview with Dr Robert N. M. Watson on research into the hardware-software interface.
- IEEE Spectrum, December 2012: interview with Dr Robert N. M. Watson on clean-slate research for security.