
Security for Ubiquitous Computing
[ Top | Reviews | Book extracts | Bibliography | A top class text | Buying | Bibtex | Dedication | Courses |Errata ]
Ubiquitous computing (ubicomp) is about networked microprocessors embedded in everyday objects: not just cellphones and home appliances but also books, bookshelves, bus stops and bathtubs--all talking to each other over wireless links. Hundreds of internet-enabled computers per human being, none of them resembling a conventional keyboard-and-monitor machine. This future is closer than you might imagine.
The insecurity of networked PCs is notorious. If the ubicomp systems we deploy in our homes, offices, shops and vehicles are as vulnerable as today's PCs, the risks for society will be catastrophic. How can we do better, and what are the new problems? Now is the time to find out, before the first generation of ubicomp systems is deployed and locks us down with backwards compatibility shackles. In a very accessible style, this book provides a coherent framework to make sense of the many issues at stake.
I wrote this book to raise awareness, so I am not addressing an audience of specialists. Instead, I speak to anyone with a technical background with an interest in these topics. I treat my readers as intelligent and alert (this is not a "for dummies" book), but I don't require any specific domain knowledge. I have included an extensive primer on the current status of ubicomp research in chapter 2 and a simple but rigorous introduction to computer security mechanisms in chapter 3. Having established this common ground, the rest of the book explores the new security issues that come up in the ubicomp scenario, sometimes offering new technical solutions, and always giving you a mental key to assess and evaluate any new problems that you might discover for yourself.
Security for Ubiquitous Computing combines clarity, brevity and authority. It will appeal to developers and researchers in ubiquitous computing, wireless and ad hoc networking, wearable computing and related areas. Because it is readable and self-contained, it will also prove valuable to managers, analysts, technology watchers and end users who want to understand the new opportunities and risks of ubicomp.
Great book - 5/5 stars
This is an excellent book and well written. It sits between being a book on UbiComp and one on security and does a great job of explaining both fields to each other. The examples chosen are from the authors own history and so he speaks with authority on them. The author is balanced in that he gives the minus points on various technologies etc as well as the plus points.
After an introduction the author spends two chapters explaining UbiComp and security from a general perspective. Both are well written and require no prior knowledge. He then in the remaining chapters goes on to address the particular security concerns in the UbiComp environment.
I thoroughly recommend this.
(Dr. Smart is author of Elliptic Curves in Cryptography, Cambridge University Press, 1999.)
This book is of wider interest than its title suggests - 4/5 stars
The book offers a lot more than its title suggests. The first two chapters are good free-standing introductions to ubiquitous computing and to computer security. They provide very readable, bang-up-to-date and well-judged technical surveys of the current state-of-the-art in each topic.
These are followed by five chapters dealing with recent work on combining the two topics to produce ubiquitous computing systems that can offer security against attacks on privacy, data integrity, system availability and user identity (or anonymity if that is desired, as it is likely to be in many real-world ubicomp applications). This topic is probably the most important obstacle to the adoption of ubiquitous computing technologies. These five chapters are based largely on work done by the author and his colleagues in Cambridge and elsewhere. The work is focussed by the special constraints and requirements that arise when building useful systems from computers that are worn by their users or are embedded in the environment, all communicating over ad-hoc wireless links. These constraints include the need to use very compact, lightweight computing devices with very low power consumption, dictating devices relatively low computing power and hence requiring algorithms of limited complexity and that conserve power.
The book is rounded off by two very solid appendices giving supporting material on the uses of mathematical functions and on the secuirty of existing computer networking technologies (including the 802.11 and Bluetooth varieties of wireless network).
The author has a talent for making descriptions of quite complex technology palatable (often even humorous) through the use of analogy, metaphor and other forms of allusions to the non-digital world. For example, the section titles 'The Resurrecting Duckling security policy' and 'The Cocaine Auction Protocol' are delightfully light-hearted, but they accurately paraphrase their contents - the exploration of a metaphor for device ownership that is based on Konrad Lorenz's thesis of parenthood by imprinting that he first demonstrated in ducklings, and a discussion of a protocol for auctions selling to anonymous bidders.
As is in all good books on advanced technical topics, the author leads the reader into an understanding of the research problems by describing currently understood solutions in a manner that leads the reader to consider how they might be taken further. The author also brings the social and commercial implications of the technologies he introduces to the fore, as for example by following the above mentioned section with a short discussion on 'Do auction houses have a future?'
(Prof. Coulouris is author of Distributed Systems - Concepts and Design, Addison Wesley, 3rd ed 2000.)
Excellent book - 5/5 stars
This book is understandable by both the technical and lay person. It provides an overview of what UbiComp is including many real life examples. Then goes on to give examples of the security violations that could result from these technologies. Some of them obvious and others pretty insightful (especially the one about RFID tags).
The book then delves into general security concepts in more detail and finishes off with some greatly named concepts: "The resurrecting duckling policy" and "the cocaine auction protocol".
The appendix has a review on some math if you want to learn it or refresh your memory.
The writing style is very clear and peppered with examples. This book as no ambiguous notation. That in itself is impressive for any technical volume. Amazingly, all that is contained in this very thin book.
Great for researchers and anyone into ubiquitous computing - 4/5 stars
Great for researchers and everyone who is interested in ubiquitous computing, which may very well be the future of computing. The book in general gives a high-level overview of available technology and security issues/requirements needed for this technology. One drawback is that the book will probably become obsolete after sometime as ubiquitous computing is evolving relatively fast.
Thanks to the wisdom and flexibility of my publisher, I am pleased to say that you may read a substantial fraction (about a third of the page budget!) of the book online, for free, before deciding to buy it.
If you have problems viewing a PDF document in your browser, it's probably the fault of a well-known bug of M$ Internet Explorer. In that case try saving the PDF to a file and viewing it from the local disk. Other solutions include changing browsers or configuring Acrobat as a helper application instead of as a plugin.
In addition to this, in memory of my former workplace which was recently shut down by the parent company, I am also offering a PDF file with the substantial and heavily illustrated section of chapter 2 ("ubiquitous computing") that I devoted to it: Section 2.5: ORL/AT&T Labs Cambridge.
A very condensed version of the main topics developed in the book appeared in April 2002 in the first Security and Privacy supplement to IEEE Computer magazine. The article, "The Resurrecting Duckling: Security Issues for Ubiquitous Computing", which I wrote with Ross Anderson, is available for free on the IEEE web site.
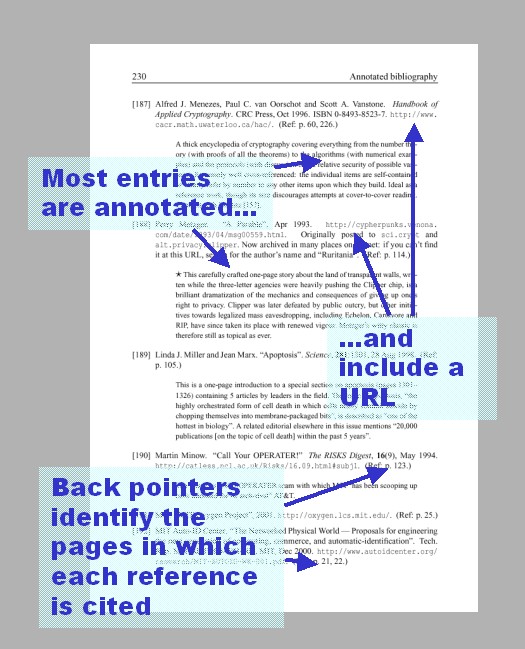
An important resource of the book is its rich bibliography, containing over 250 entries. Apart from full bibliographic details, most entries include an annotation and a URL. There are even back references from the bibliography into the main text; so, if one of the annotations tickles your curiosity, you may go back to the body of the book to examine the context in which it was brought up. (I wish more books had this feature!)
At all the stages of the production of this book the response from the people who had to evaluate it has been very enthusiastic. The Wiley reply to my book proposal started by saying
It is one of the best written proposals I've had in a long time!
The internal Wiley panel that had to evaluate the proposal approved it unanimously. Following this, I was immediately offered a contract and started working on the text. The many (17!) friends who reviewed my drafts sent in lots of appreciative and encouraging comments. Months later, while I was putting the finishing touches to the book, between the intermediate deadline for a reviewable copy and the final deadline for the completed manuscript, I got the following email from my editor.
Hello Frank,
I have really, really good news. After sending your manuscript to a very direct and competent reviewer, here is his feedback:
"Basically, this is a top class text. There is very little I could do to proof read it as it is already way better than I could propose. It oozes authority, is well put together and covers all of the areas I'd hope to see.
What more can I say?
So nice to see a really good one!"I have to confess that I have not ever, ever had such positive feedback on any manuscript. I am amazed!
Congratulations!
Now I look forward to the feedback from my actual audience! The book was written for my readers, not for my publishers, and I spared no effort to make this book interesting for you. I hope that you will enjoy it, that you will find it clear, concise and informative, and that you will learn something from it that will be useful and valuable to you. If there's anything you didn't like, please let me know so that I can do better next time (and/or in my lectures). But of course, if you like as it is, I'm always happy to hear about that too!
If you wish to comment on the book, feel free to write to me at fms27@cam.ac.uk. Or, even better, if you wish to make your comments public, post them to amazon.com.
Now there's a really smart move ;-) Your local technical bookstore is likely to carry this title, especially if it sells any other Wiley books. If, however, you prefer to buy it online, you may try several places including Wiley Europe, Barnes and Noble and Amazon.com or .co.uk. Some of these outlets may also offer special discounts for limited periods. In theory, BestBookBuys surveys and lists any special offers; in practice the information on their site is not always reliable, though it may still give you useful clues and pointers.
Frank Stajano, University of Cambridge (UK)
Security for Ubiquitous Computing
John Wiley and Sons, Ltd
Wiley Series in Communications Networking & Distributed Systems
ISBN: 0-470-84493-0
Hardcover; pp. 267 (xx + 247)
Publication date: 2002-02-12
@book{2002-Stajano-ubiquitous,
author={Frank Stajano},
title={Security for Ubiquitous Computing},
publisher={John Wiley and Sons},
year=2002,
month=feb,
isbn={0-470-84493-0},
url={http://www.cl.cam.ac.uk/~fms27/secubicomp/},
}
This book is dedicated to the memory of the great storyteller Carl Barks (1901-2000), perhaps the greatest comics author of all times, who invented the inventor Gyro Gearloose. Gyro was into ubiquitous computing many decades before Mark Weiser coined the term.
Here are some of the lecture courses taught around the world that adopt this volume as a recommended textbook.
Negative line numbers are counted from the bottom of the page. If you have found an error not listed here, please tell me about it by writing to fms27@cam.ac.uk with a subject of "Errata corrige for secubicomp".
| Page | Line | Errata | Corrige | Found by | On |
|---|---|---|---|---|---|
| xx | 6--7 | but don't trust them as mine unless they have been signed by both of the keys below. | and for those you'll have to check for a chain of signatures---with all the keys in the chain belonging to me, and with the root of the chain being the keys printed below. | author | 2002-02-28 |
| 8 | -14 | IBM Systems Journal | IBM Systems Journal | author | 2002-04-09 |
| 64 | -16 | lead | led | author | 2021-01-29 |
| 126 | -10 | in a later packet Mi+d. | in a later packet Pi+d. | author | 2004-01-12 |
| 126 | -8 | so long as you receive Mi before Mi+d | so long as you receive Pi before Pi+d | author | 2004-01-12 |
| 159 | 7 | ways in we might | ways in which we might | Alastair Beresford | 2003-09-05 |
| 170 | -8 | B={J, Q, K} | A={J, Q, K} | author | 2002-01-21 |
[ Top | Reviews | Book extracts | Bibliography | A top class text | Buying | Bibtex | Dedication | Courses |Errata ]